Critical infrastructure is more vulnerable than ever. It doesn’t have to be that way
[edit] Introduction
Subway cars stuck in a tunnel. Electricity blackouts. A breached dam. Jammed telecommunications. These and other potential consequences of critical infrastructure security breaches can at best cause only inconvenience; at worst, they can lead to death or destruction on a shocking scale. Power outages in the Ukraine in 2015 and 2016 represent two such cases in point.
In today’s hyperconnected world, such infrastructure is more vulnerable than ever to cyber security threats, whether from nation states with bad intentions, criminal organisations or individuals.
This new vulnerability stems from fundamental changes in the critical infrastructure of organisations’ technology systems. Such organisations — healthcare providers, utilities, chemical producers, manufacturers, defence agencies, first responders, banks, transportation systems — have long owned and operated two types of technology systems.
Their information technology systems run basic office functions, such as email, payroll and human resources systems; while their operational technology (OT) systems control physical equipment and personnel essential for carrying out their mission, such as generating and transmitting power.
In the past, OT consisted of stand-alone systems that used little-known, proprietary protocols — their very obscurity made them secure. But now, OT systems run on the same commonly-known software and hardware platforms as IT systems. These systems are well understood by hackers and therefore significantly less secure.
[edit] Unprecedented exposure
What has led to this convergence of OT with IT? It’s the growing demand for seamless access to information — access that hinges on the use of smart digital technologies, including sensors, cameras and wearables. For instance, a utility gathers online data on power outages from smart meters so it can swiftly identify problem locations and restore power to customers.
A homeowner remotely adjusts the thermostat at her residence to lower the temperature while she’s on vacation. A doctor views patients’ insulin use on an office computer. Companies remotely monitor the status and location of trains, buses and trucks; the flow of oil and gas through pipelines; or water or electricity consumption to manage these services effectively and efficiently.
While the technologies in these examples improve our lives and infuse efficiencies into our economy, they can also make us more vulnerable. When customers of three Ukrainian power utilities lost power because of a cyber incident, those utilities were able to fall back on manual operations to restore power. This would not be possible in a number of other countries where manual operations no longer exist.
When a hospital in Los Angeles experienced a Ransomware attack, which locked up the hospital systems and made them unavailable, the hospital temporarily lost information about medications prescribed to patients. Fortunately, no one died from receiving the wrong medication or not receiving the right medication.
As the number of interconnected devices continues to increase, the number of potential access points for hackers to disrupt critical infrastructure grows as well. All of these devices need to be designed, implemented and deployed in ways that make them less vulnerable to attacks.
In short, dependence on technology is now critical and increasing exponentially. When attackers strike the systems that use those technologies, being inconvenienced or annoyed may constitute the very least of the worries.
[edit] Understanding the challenges
Today’s high levels of interconnectivity and exposure have also spawned serious challenges for critical infrastructure organisations, as BCG Platinion explained to the US Presidential Commission on Enhancing National Cybersecurity in a report submitted to the National Institute of Standards and Technology (NIST). Let’s take a closer look.
[edit] The need to secure future digital infrastructure while it’s still evolving
Smart cities, technology-enabled medicine and driverless cars carry a wonderful promise of better, safer and more productive lives for all. But to build the digital infrastructure required to fulfil this promise, critical infrastructure organisations must anticipate the future needs of such infrastructure.
Some of the technologies that the infrastructure will have to support have not yet been invented. It’s akin to building an airplane without knowing how far it will have to fly and how many people it will carry.
To make matters even more difficult, critical infrastructure organisations’ OT systems consist of older technologies that were designed and implemented before cyber security was on anyone’s radar. Because these systems are critical, they frequently cannot be taken offline for redesign and repair. What’s more, replacing that installed base is costly and time consuming. It is hard to imagine shutting down the electricity to a neighbourhood for six months to do an upgrade.
[edit] Cyber security talent deficit
Ensuring that smart devices are designed, implemented and maintained with security in mind is not easy. Furthermore, it requires specialised expertise that are in short supply globally. The global deficit of cyber security expertise is well documented. Finding those who know how to secure both IT and OT systems required by critical infrastructure is even more difficult.
Although the technology underlying the two types of systems is now the same, securing both types of systems entails different priorities and different approaches. The difference in priorities is pronounced: OT systems must first and foremost be safe and available, while IT systems must first and foremost protect confidentiality of the data that they process and store.
People who spend their careers in IT or OT environments are driven by these very different priorities, usually have different educational backgrounds, and, as a result, have very different mindsets. Finding people who can practise both OT and IT cyber security is no small feat, while cross-training is difficult, costly and not always successful.
[edit] Resource disparity between large and small organisations
Cyber security is a complex discipline comprising multiple knowledge areas. Doing it right requires a variety of specialised expertise that smaller organisations cannot afford.
Large critical infrastructure organisations with hefty resources can hire their own experts and set up sophisticated cyber security programmes. Smaller ones (like emergency response agencies and water utilities) have to manage the same risks with significantly fewer resources.
[edit] Reliance on third parties to deliver critical capabilities securely
The laws of economics drive businesses to focus on core competencies and outsource the rest. So it’s not surprising that transportation companies, utilities, healthcare providers, financial services providers and countless other industries rely on numerous partners to deliver anything from software and hardware, to legal or consulting services. That includes the hardware and software components of critical infrastructure and the multitude of smart devices.
Companies that merge are integrated much more tightly than in the past, including interconnecting each other’s systems and exchanging highly sensitive information. To make matters more complicated, suppliers have their own suppliers, sub-suppliers, and so forth.
The supply chain has therefore become a supply network — long, extended, complex, multidimensional and multinational. This provides an almost infinite number of additional points that can be compromised. While traditional IT manufacturers have been dealing with cyber-threats for 20 to 30 years, smart device and critical infrastructure systems manufacturers have only recently been introduced to the problem.
The cyber security workforce shortage discussed earlier has a significant impact on suppliers’ ability to secure their devices, including securing their own supply chains. Suppliers that used to make manually-operated hardware devices and that now make software-driven smart devices, have to learn about cyber-security quickly.
[edit] Taking action: our recommendations to the Presidential Commission
Internet time advances much more swiftly than people time. That is, threat actors move in internet time, while people think, analyse, and agonise over decisions. Organisations must act now to mitigate the cyber security challenges facing them today. We’ve developed several recommendations for contributing to effective, collective action.
IT/OT cyber security-practitioner development is a case in point. While federally-funded cyber security workforce development programmes are a step in the right direction, they focus on general cyber security training, not IT/OT environments. They therefore don’t fully address the needs of critical infrastructure organisations in industries like manufacturing, transportation, and utilities — or their supplier ecosystems.
To help close the gap, organisations can support the creation of a broader range of educational approaches, including college degrees, apprenticeship programmes and IT/OT security training for existing employees.
Cross-organisational mentoring and knowledge transfer is another recommendation. Organisations with less cyber security experience or smaller cyber security teams can learn from the experiences of their more seasoned peers. Larger organisations should also encourage their experts to participate in industry associations, public-private partnerships, and regional organisations, which all provide opportunities for formalising cross-organisational mentoring and knowledge transfer.
Smaller organisations should encourage similar participation. In the short term, such working groups take time away from people’s day jobs. But in today’s interconnected world, organisations will benefit in the long run, because the knowledge transfer will improve the security of the infrastructure that connects them.
[edit] Embedding cyber security into organisational culture and strategy
In addition to the recommendations described above, critical infrastructure organisations must weave cyber security into their very culture and strategy planning. As with safety and quality programmes, these efforts will call for large-scale, transformative change.
Organisations can’t just rely on adopting cyber security technology solutions. Instead, they must set up the right incentives, performance management, training, processes, procedures and other systems, to ingrain the mind-set, behaviour and practices that cyber security requires. This includes using existing technologies effectively and enforcing new policies. On a more detailed, day-to-day level, executives need to lead by example, demonstrating the thinking, actions and values that they want others throughout their organisation to emulate.
In short, the most effective way to increase cyber security resilience is by changing the way people use technology – not by adding technology to compensate for technologies that are not being properly used.
Most of the categories in NIST’s Cybersecurity Framework are non-technical, supporting this fact. Indeed, we recommend the following practices, inspired by our work with MIT, the World Economic Forum and companies around the world, as crucial for weaving cyber security into an organisation’s culture and strategic planning:
- Empower your top cyber security leaders by giving them authority, budget, and regular access to your organisation’s board of directors.
- Acquire appropriate expert support — internally and externally.
- Define your cyber-risk tolerance consistently with your business strategy and risk appetite.
- Support cyber security investments that maximise business impact.
- Require reports containing achievable information that supports effective, prioritised decision-making.
- Establish clear communications and accountability to encourage collaboration across the enterprise.
- Support cyber security collaboration and information-sharing with third parties, including customers, suppliers, business partners and competitors.
In the end, organisations that integrate cyber security into their culture and strategic planning will be the most resilient. Everyone in the organisation will understand what cyber security means; why it matters to their organisation, society at large, their jobs, and their families; and how they, in their everyday work and interactions, can make a difference in securing the entire nation’s critical infrastructure. Hard work? Most certainly. But no critical infrastructure organisation can afford to shy away from it.
Written by:
- Nadya Bartol, Associate Head of Cybersecurity Practice, BCG Platinion
- Michael Coden, Head of the Cybersecurity Practice, BCG Platinion
The views expressed in this article are those of the author alone and not the World Economic Forum.
This article was originally published on the Future of Construction Knowledge Sharing Platform and the WEF Agenda Blog
--Future of Construction 14:33, 20 Jun 2017 (BST)
[edit] Find out more
[edit] Related articles on Designing Buildings Wiki
- Big data for buildings
- Cyber threats to building automation and control systems.
- Digital communications and infrastructure dependencies.
- Engineering resilience to human threats.
- Infrastructure and cyber attacks.
- Intelligent building management systems IBMS.
- Security and the built environment.
- Smart buildings.
- Trends towards wearables and wellbeing in buildings.
- Vital infrastructure and redevelopment.
Featured articles and news
Key points for construction at a glance with industry reactions.
Functionality, visibility and sustainability
The simpler approach to specification.
Architects, architecture, buildings, and inspiration in film
The close ties between makers and the movies, with our long list of suggested viewing.
SELECT three-point plan for action issued to MSPs
Call for Scottish regulation, green skills and recognition of electrotechnical industry as part of a manifesto for Scottish Parliamentary elections.
UCEM becomes the University of the Built Environment
Major milestone in its 106-year history, follows recent merger with London School of Architecture (LSE).
Professional practical experience for Architects in training
The long process to transform the nature of education and professional practical experience in the Architecture profession following recent reports.
A people-first approach to retrofit
Moving away from the destructive paradigm of fabric-first.
International Electrician Day, 10 June 2025
Celebrating the role of electrical engineers from André-Marie Amperè, today and for the future.
New guide for clients launched at Houses of Parliament
'There has never been a more important time for clients to step up and ...ask the right questions'
The impact of recycled slate tiles
Innovation across the decades.
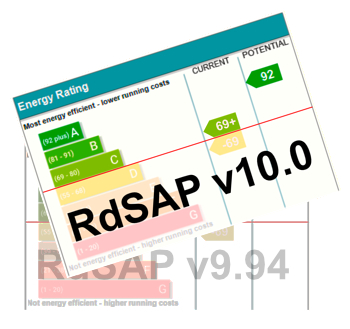
EPC changes for existing buildings
Changes and their context as the new RdSAP methodology comes into use from 15 June.
Skills England publishes Sector skills needs assessments
Priority areas relating to the built environment highlighted and described in brief.
BSRIA HVAC Market Watch - May 2025 Edition
Heat Pump Market Outlook: Policy, Performance & Refrigerant Trends for 2025–2028.
Committing to EDI in construction with CIOB
Built Environment professional bodies deepen commitment to EDI with two new signatories: CIAT and CICES.
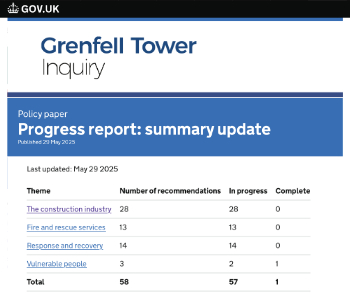
Government Grenfell progress report at a glance
Line by line recomendation overview, with links to more details.
An engaging and lively review of his professional life.
Sustainable heating for listed buildings
A problem that needs to be approached intelligently.
50th Golden anniversary ECA Edmundson apprentice award
Deadline for entries has been extended to Friday 27 June, so don't miss out!
CIAT at the London Festival of Architecture
Designing for Everyone: Breaking Barriers in Inclusive Architecture.
Mixed reactions to apprenticeship and skills reform 2025
A 'welcome shift' for some and a 'backwards step' for others.