Security and the built environment
Contents |
[edit] Introduction
There are an increasing number of terrorist and cyber-attacks targeted at our largest and most treasured institutions and companies.
Terrorism by its very nature is highly visible and can make people feel vulnerable when they are in public places, at work or away from home. This anxiety has made end users and a range of professionals involved in the procurement and management of real estate ask many more security related questions. Questions such as:
- Are we a target?
- Are we secure?
- Should we install CCTV, fences, or deploy additional guards?
- Do we need to invest more in security?
Generally, people are looking for some level of reassurance. They want to know what others are doing:
- Are they changing the way they secure their facilities?
- Are they spending more on security?
- What innovative solutions are available to address the latest threats?
Ultimately, people do not want to fall behind their peers. This in itself can make their estate a more attractive target and them as individuals personally liable where failings are identified following an incident.
Unfortunately, these questions often come from people at the coal-face, people that can implement better security but only when they are able to access appropriate resources to implement improvements.
[edit] Businesses and security
Generally speaking, facility security managers will be representing one of two types of enterprise, those that are:
- Security conscious, i.e. organisations that inherently value security due to the nature of their business and are therefore willing to invest.
- Indifferent towards security, i.e. organisations that do not necessarily see a link between security and the success of their business and therefore ask, why should I invest?
Understandably, business leaders have a range of competing issues to address to make their businesses successful. If a business wants to be secure, it needs to ask for security and fund it. This needs to come from the top in the form of a commitment to operate securely for the benefit of staff, customers and other stakeholders. In some sectors, such as energy, aviation and communications, this is par for the course.
Senior executives will know that if they fail to establish an effective policy, comply with the regulations or give stakeholders confidence in their ability to operate safely and securely, they won't have a business and will struggle to attract custom and investment. In these environments, it is essential to establish a security culture, as security is core to the success of the business.
These businesses can be recognised by looking at corporate strategies and financial reporting. Security will feature in strategic priorities, principal business risks and uncertainties. These are the businesses that will be best placed to weather the storm.
In the other camp, security is not traditionally recognised as a core factor in determining business success. Financial reports for these businesses will focus on profit and loss but not security. These businesses were probably vulnerable before and will remain vulnerable. However, now the threat has increased, so have the risks to their business.
The big question is, regardless of the nature of a business, can any organisation afford to ignore the risks associated with these security threats?
All businesses, from SMEs to large corporates, need to be security conscious for a range of reasons, including:
- Dependency on data, energy, complex systems and people to maintain operations.
- Rapid communication of incidents via traditional media outlets and social media that can quickly impact on reputations.
- High consumer expectations. A just-in-time approach to manufacturing and delivery of services, which can quickly damage confidence when things go wrong.
- Health and safety legislation and data protection requirements which apply to all.
As a result, security performance, like business finances, should be monitored, assessed, evaluated and reported. This requires a change in many boardrooms and unfortunately many organisations are unlikely to change until they see further examples of reputational damage, lost earnings and eroded trust in their sectors or even in their own business.
If you have considered ramping up your facility's security, you are probably struggling to get additional resources to implement your plans and even if you try, you may face push back from end users. Fundamentally, very little will change at a local level without enterprise direction and support, regardless of the security context.
[edit] How should you proceed?
The following points apply whichever type to all organisations and will help you assess the current situation and what might need to be done in the future.
[edit] Understand your security needs
- What assets do you have at your facility?
- How much security can you realistically implement without impacting on operations?
- Who uses your facility, when and what level of access is required?
- Do you have obligations to any third parties?
[edit] Understand the risks
- What threats are relevant to your types of facility?
- How does the geographical location and local setting influence the likelihood of an incident?
- Is your facility iconic or does it have attributes that make it an attractive target?
- Who might attack you, when and how?
- How vulnerable is the facility to these types of incidents?
- What consequences may result in the event of an incidents?
Through the analysis of these issues, you will be in a position to determine whether any action is required or at least if further assessment is required. If you have not considered these factors, then there is little assurance that your existing facility security is effective or that any planned investment will deliver tangible improvements.
This information can be used to communicate local issues to senior management. Risk communication will assist you in making a case for improvement and in some cases may even highlight cost savings if existing measures do not contribute to better security outcomes.
[edit] What security improvements should you implement?
There is no silver bullet to address the likes of 'lone wolf attacks' and the police certainly cannot be everywhere, all of the time. Your approach to securing your facility will naturally be dependent on the results of your risk assessment. The measures you adopt should be focused on reducing vulnerabilities and consequences, i.e. improved protection.
Never implement security for security's sake. It is disappointing to see significant investment in measures that do not contribute to improved security. This can result in a false sense of security for occupants and is purely 'security theatre'. In some cases, it may be possible to deter certain types of crime through visible security features but it will be difficult to measure their value. If in doubt, always seek professional advice.
An effective facility security can be achieved through the following:
[edit] A strategic approach
You should have a written policy and a supporting security strategy that set out what you are trying to achieve and ensure that security measures meet operational requirements. This will allow you to remain focused on your objectives and ultimately measure performance.
[edit] System-level thinking
You must be careful not to focus solely on physical and technical security features that could quickly absorb your entire security budget. Recent events have shown how quickly threats can change. How you might be attacked tomorrow may be very different to the methods used in recent attacks. Criminals and extremists have shown that they can use very simple tactics to achieve their goals or embark in complex organised cyber crimes which the average person may not even understand, let alone anticipate.
The built environment is traditionally slow to adapt, with physical changes being time consuming, expensive and disruptive to implement. It is important to achieve balance by integrating personnel security, cyber security and physical security. This requires leadership, cooperation and coordination.
[edit] Risk Management System
Establishing a security risk management system will help get the most out of your security budget. It will provide a framework for effective security and enable you to evidence the steps you have taken to mitigate risks.
In a security conscious organisation, there may be an enterprise level risk management system. In this case, your local management system should be aligned with that of the organisation. Where this is not the case, you may wish to establish your own system.
[edit] Tried and tested incident management and recovery plans
Far too often, security planning stops at the point of incident detection or an incident plan may rely solely on the police for incident response. It is important that having detected suspicious behaviour or a loss at the facility, there is appropriate infrastructure and procedures in place to communicate with interested parties and manage the incident. This might require on-site personnel to take response and recovery actions in order to mitigate losses.
Having invested significant time and resources in mitigating security risks, it is important to communicate facility's security credentials and provide stakeholders with assurance of your capability. This might be required internally within some organisations, it may be a regulatory requirement for your sector or may act as a differentiator that offers competitive advantage.
This article was originally published by BRE Buzz in July 2016. It was written by Gavin Jones. You can see the original article here.
--BRE Buzz
[edit] Related articles on Designing Buildings
- 2021 survey on public safety in crowded places.
- Access control.
- Access to construction sites.
- Approved document Q.
- Barrier.
- Bollard.
- BREEAM Safety and security.
- BRE Buzz articles on Designing Buildings Wiki.
- CCTV.
- Crime Prevention Design Advisor.
- Critical infrastructure is more vulnerable than ever. It doesn’t have to be that way.
- Defensible space.
- Electric lock.
- Embedded security: Procuring an effective facility protective security system.
- Entry control.
- External doors.
- Fire detection and alarm systems.
- Hostile architecture.
- How to install an underfloor safe.
- Infrastructure and cyber attacks.
- Insurance.
- Intruder alarm.
- Mortice lock.
- Outbuildings security.
- Panopticon.
- Perimeter security.
- SABRE Security Assurance by the Building Research Establishment.
- Secured by design.
- Secure space.
- Security after COVID-19.
- Security consultant.
- Security glazing.
- Security rating scheme.
- Smart surveillance, video surveillance and VSaaS.
- Suitably qualified security specialist.
- Types of alarm.
- Types of lock.
Featured articles and news
We're expanding our collaborative mission by launching DB Intelligence, an exclusive market research advisory panel. Built environment professionals can now get paid to share their expertise on industry trends, products and services.
Panel members receive direct financial incentives for participating in research projects like short surveys, 1-2-1 interviews and focus groups. Register today to shape the future of the construction sector.
Building Control Independent Panel final report
A precis of a key report led by Dame Hackitt with full recommendations and link to the government response.
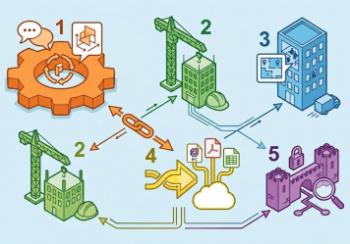
Guide to ISO 19650 for Architecture Firms (2026)
A user gives their low down.
A UK training and membership provider for mould remediation professionals.
Building Safety recap April, 2026
A short and longer run-through of the month, with links to further information and sources.
CIAT May 2026 briefing.
Independent NSI and BAFE study exploring how organisations are changing the way they buy fire safety services.
From medieval scribes to modern word art.
ECA welcomes crackdown on late payment and push for clean energy, whilst CIOB seek fixed cladding removal timeframes.
Cyber Security in the Built Environment
Protecting projects, data, and digital assets: A CIOB Academy TIS.
Managing competence in the built environment
ITFG publishes new industry guide on how to meet the ICC principles.
The UK's campaign to reduce noise pollution: Mythbusting, articles and topic guides.