About Shubham1313
Title: Ethical Hacking vs. Malicious Hacking: Key Differences
Introduction
In a world increasingly reliant on digital technologies, the concept of hacking has become an integral part of our vocabulary. However, hacking isn't a monolithic practice; it encompasses a broad spectrum of activities, some ethical and necessary for cybersecurity, while others are malicious and harmful. In this blog, we'll delve into the key differences between ethical hacking and malicious hacking, shedding light on the motivations, methodologies, and implications of each. Ethical hacking course in Pune
Understanding Ethical Hacking
Ethical hacking, also known as penetration testing or white-hat hacking, refers to the practice of intentionally probing computer systems and networks to uncover vulnerabilities and weaknesses. Ethical hackers are authorized professionals hired by organizations to simulate cyberattacks on their systems, with the goal of identifying and patching security flaws before malicious hackers exploit them. Here are some key characteristics of ethical hacking:
- Authorized and Legitimate: Ethical hackers have explicit permission to assess the security of a system. They work under legally binding contracts and follow strict rules and guidelines.
- Beneficial Intent: Ethical hackers aim to improve security and protect sensitive data. Their primary objective is to help organizations strengthen their defenses against cyber threats.
- Legal Boundaries: They operate within the boundaries of the law, respecting privacy and data protection regulations.
- Transparency: Ethical hackers provide detailed reports of vulnerabilities and recommended fixes to the organizations they work for.
- Continuous Learning: Ethical hackers stay up-to-date with the latest security trends and tools to ensure their skills are effective in countering emerging threats.
Exploring Malicious Hacking
On the flip side, malicious hacking, often referred to as black-hat hacking, represents the dark underbelly of the digital world. These hackers engage in illegal activities with the intent to exploit vulnerabilities for personal gain or harm. Here are some defining characteristics of malicious hacking:
- Unauthorized: Malicious hackers infiltrate systems without permission, breaking the law in the process.
- Malicious Intent: Their actions are driven by personal gain, financial profit, or causing harm. This can include stealing data, spreading malware, or disrupting services.
- Illegal: Malicious hacking activities are criminal acts, subject to severe penalties when caught and prosecuted. Ethical hacking classes in Pune
- Anonymity: Malicious hackers often take measures to hide their identities, making it challenging for authorities to trace them.
- Exploitative: Unlike ethical hackers, malicious hackers do not disclose vulnerabilities to the affected organizations. Instead, they exploit these weaknesses for their own benefit.
Key Differences
Now that we've established the fundamentals of ethical and malicious hacking, let's highlight the key differences between the two:
- Authorization: Ethical hackers have explicit permission to assess systems, while malicious hackers operate without authorization.
- Intent: Ethical hackers seek to improve security, whereas malicious hackers aim to exploit vulnerabilities for personal gain or harm.
- Legality: Ethical hacking is legal and conducted within the bounds of the law, while malicious hacking is illegal and subject to legal consequences. Ethical hacking training in Pune
- Transparency: Ethical hackers provide detailed reports to organizations, helping them bolster their defenses. Malicious hackers operate covertly, without disclosing their activities.
- Moral and Ethical Considerations: Ethical hackers adhere to a code of ethics, prioritizing the greater good and data protection. Malicious hackers lack these ethical constraints.
Featured articles and news
A safe energy transition – ECA launches a new Charter
Practical policy actions to speed up low carbon adoption while maintaining installation safety and competency.
Frank Duffy: Researcher and Practitioner
Reflections on achievements and relevance to the wider research and practice communities.
The 2026 Compliance Landscape: Fire doors
Why 'Business as Usual' is a Liability.
Cutting construction carbon footprint by caring for soil
Is construction neglecting one of the planet’s most powerful carbon stores and one of our greatest natural climate allies.
ARCHITECTURE: How's it progressing?
Archiblogger posing questions of a historical and contextual nature.
The roofscape of Hampstead Garden Suburb
Residents, architects and roofers need to understand detailing.
Homes, landlords. tenants and the new housing standards
What will it all mean?
The Architectural Technology podcast: Where it's AT
Catch-up on the latest episodes.
Edmundson Apprentice of the Year award 2026
Entries now open for this Electrical Contractors' Association award.
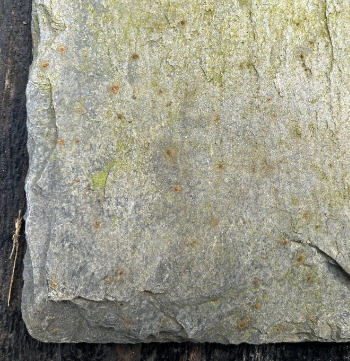
Traditional blue-grey slate from one of the oldest and largest UK slate quarries down in Cornwall.
There are plenty of sources with the potential to be redeveloped.
Change of use legislation breaths new life into buildings
A run down on Class MA of the General Permitted Development Order.
Solar generation in the historic environment
Success requires understanding each site in detail.
Level 6 Design, Construction and Management BSc
CIOB launches first-ever degree programme to develop the next generation of construction leaders.
Open for business as of April, with its 2026 prospectus and new pipeline of housing schemes.
The operational value of workforce health
Keeping projects moving. Incorporating unplanned absence and the importance of health, in operations.